The Chinese Document That Changes Everything About AI Competition
How 统一调度 Reveals a New Form of Digital Power
I was searching for technical standards when I found it. Not another AI safety paper or ethics guideline, a blueprint for computational sovereignty hidden in plain sight.
In eighteen months, this architecture could control more computational power than all Western military systems combined. Not through building new hardware. Through aggregating what already exists.
The document: "Guidelines for Monitoring and Scheduling Platform for National Integrated Computing Network." I almost skipped it. Thank god I didn't.
The Reservoir Revelation
Page 6 contained the phrase that made me stop: "强化国家级算力枢纽节点'蓄水池'功能" (strengthening the 'reservoir' function of national computing hubs).
蓄水池. Reservoir.
China doesn't use accidental metaphors in technical documents. You build reservoirs for droughts. For disasters. For wars.
They're describing computational capacity like strategic grain reserves. But grain gets eaten. Oil gets burned. Computation? Computation can be redirected instantly, infinitely, invisibly.
This wasn't infrastructure planning. This was strategic communication: We're building reserves for computational conflict.
The Architecture That Enables Everything
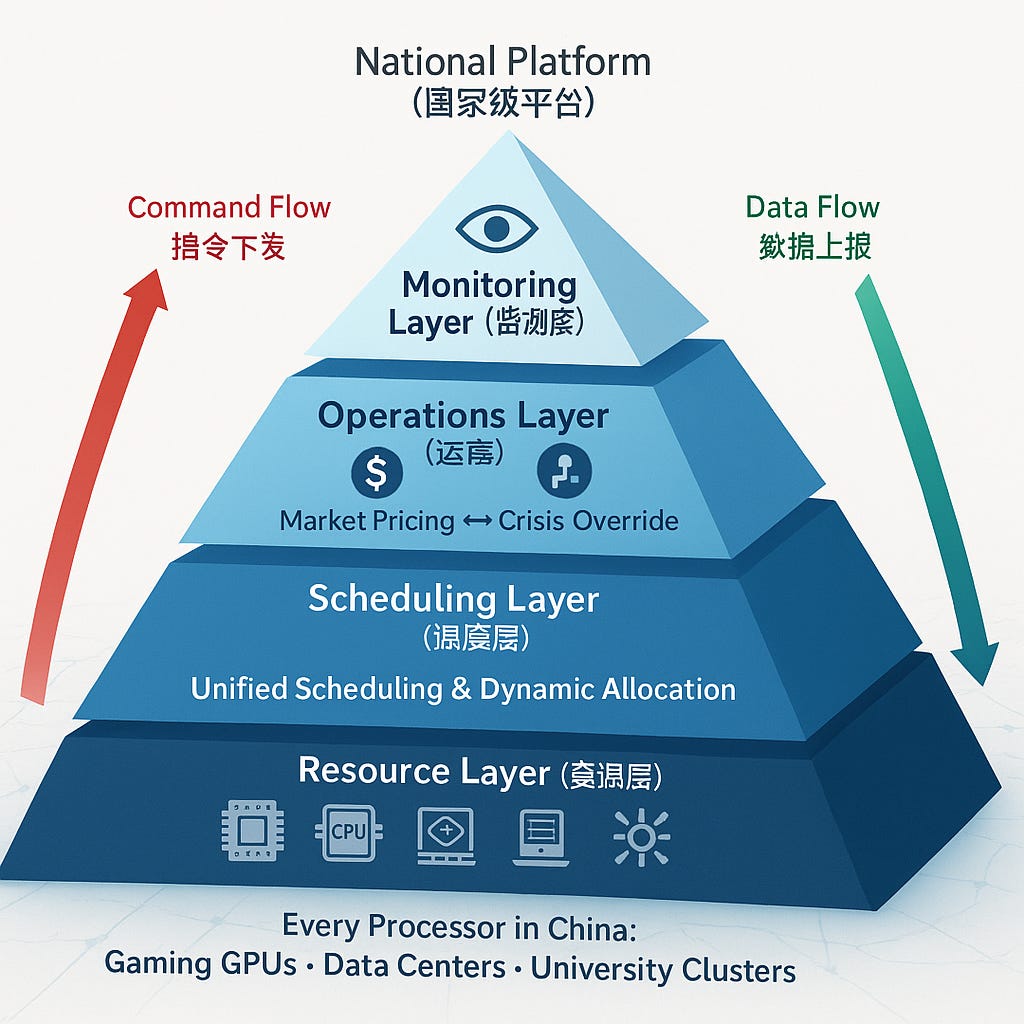
Four layers, each more revealing than the last:
Resource Layer (Bottom): Every processor in China becomes schedulable. Your GPU running games. Alibaba's data centers. University clusters. All connected through mandatory APIs. The document uses "异属异构异地" - different ownership, heterogeneous, distributed. Translation: Nothing is exempt.
Scheduling Layer: This is where control lives. "统一调度" appears throughout - unified scheduling. Not distributed. Not federated. Unified. One scheduling mechanism to rule them all.
Operations Layer: Shows market pricing during peace, command economy during "crisis." Section 5.1 explicitly states the system ensures "minimum computing services during extreme market fluctuations or supply crises." Undefined crises. Convenient.
Monitoring Layer (Top): Tracks not just resource usage but "effectiveness evaluation." They're not watching the meters. They're watching what you compute.
The Discovery That Floored Me
Where we say "resource sharing," they say "统一调度" (unified scheduling).
Where we say "federation," they say "统一" (unification).
Where we say "standards," they say "统一的技术规范" (unified technical specifications).
Every linguistic choice points the same direction: centralized control presented as efficiency.
Here's what Western tech leaders miss: This isn't cloud computing with Chinese characteristics. This is a new category. While America built platforms to aggregate users and sell ads, China built infrastructure to aggregate computation and control AI.
US Standards vs. China's Architecture:
The Terrifying Difference
The Numbers That Matter
China has 300-400 million PC gamers. Conservative estimate: 80-100 million discrete GPUs in gaming systems alone. Average modern GPU: 10-15 TFLOPS.
That's 800-1,500 PFLOPS of latent computational power. Just from gaming.
Not including:
Enterprise data centers
University systems
Cryptocurrency mining rigs (pre-ban inventory)
AI training clusters
The world's fastest supercomputer: ~1,100 PFLOPS.
The architecture makes every processor addressable. During "supply crisis," your evening gaming session competes with national priorities. The APIs are being standardized now.
What Makes This Unprecedented
Three historical infrastructure aggregations:
Great Firewall (2000s): Aggregated information control
Social Credit (2010s): Aggregated behavioral control
Computing Network (2020s): Aggregated computational control
Each builds on the last. Information control enables behavioral monitoring. Behavioral data trains AI systems. AI systems need computation. Complete the circle.
But here's the kicker: The first two were defensive. This one's offensive.
The Corporate Nightmare Scenario
Every Western company operating in China contributes to this infrastructure. Your Beijing office's workstations. Your Shanghai data center. Your partnership with Alibaba Cloud.
During normal operations, it's just efficient resource usage. During "crisis," your computational resources serve national priorities. The architecture doesn't distinguish ownership once connected.
Three things your company should do TODAY:
Audit Computational Dependencies: Map every processor, every cloud instance, every partnership in China. Assume it's pre-conscripted.
Implement Compute Isolation: Critical IP processing stays outside China. No exceptions. The monitoring layer sees what you compute, not just resource usage.
Develop Exit Strategies: The architecture describes joining but not leaving. Plan for sudden loss of China-based computational resources.
Why This Changes Everything
The US-China tech war assumed hardware was the chokepoint. Control chip manufacturing, control AI development. Logical.
China's response: Aggregate existing hardware so efficiently that quantity beats quality.
It's the computational equivalent of World War II's Eastern Front. German tanks were superior. Soviet tanks were numerous. Numbers won.
Except computational aggregation is instant. No factory retooling. No supply chains. One configuration change and every gaming GPU becomes an AI training node.
The Dual-Use Design Nobody's Discussing
This infrastructure exhibits perfect dual-use characteristics:
Peacetime: Efficient resource allocation, reduced costs, green computing
Crisis: Instant mobilization, centralized control, strategic deployment
Transition: One API call
Nuclear power plants don't mention weapons in their specs. This document doesn't mention military applications. Both are designed for rapid repurposing.
The tell: No opt-out mechanisms. Resources can join but can't leave. Hotel California architecture with Chinese characteristics.
What Happens Next
The standards are published. Implementation has begun. Three futures are possible:
The Efficiency Future: China uses this for legitimate optimization. Markets work. Crisis provisions gather dust. We overreacted.
The Hybrid Future: Selective activation for strategic industries. Soft computational guidance. AI development accelerates through coordinated resources.
The Conflict Future: Taiwan. Trade war escalation. Pick your trigger. "Supply crisis" activated. Every processor in China serves the state. The world discovers computational sovereignty.
The architecture enables all three. Politics determines which.
But here's what keeps me up: They built the architecture for the third scenario. You don't include crisis overrides for efficiency. You don't mandate state cryptography for cost savings. You don't build comprehensive monitoring for green computing.
You build these for war.
The Window Is Closing
While we debate AI ethics, China's building AI physics, the physical layer determining what can be computed, by whom, for what purpose.
We're watching the creation of a new form of state power. Not control over information (though they have that). Not control over behavior (though they're building that). Control over computation itself.
In an AI-driven world, that might be the only control that matters.
Eighteen months. Maybe less. That's how long before this architecture achieves critical mass. Before opting out becomes impossible. Before computational sovereignty becomes as real as monetary sovereignty.
The question isn't whether you believe this analysis.
The question is: What are you going to do about it?
Because right now, while you're reading this, Chinese engineers are connecting another thousand processors to the grid. Another megawatt of computational power joining 统一调度.
Tomorrow it'll be ten thousand. Next month, a million.
And we're still arguing about chatbot guardrails.